Our Processes
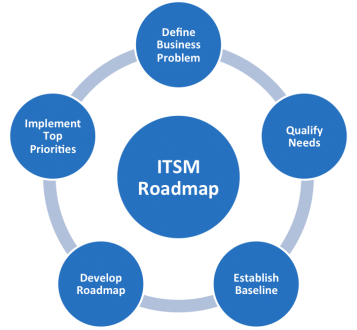
The IT Enterprise has adopted the best practices framework for IT Service Management to improve service delivery and in turn improve customer satisfaction. Working together, the processes and functions defined within ITIL focus on the entire lifecycle of a service, including Service Strategy, Service Design, Service Transition, Service Operation, and Continual Service Improvement. These processes are designed to:
- Ensure that IT Services are aligned to the needs of customers
- Improve availability and stability of services
- Improve communication within IT and with customers
- Set appropriate expectations for IT services
- Improve efficiency of internal processes
Incident Management
Overview
Part of the Service Operation lifecycle, Incident Management manages the lifecycle of all Incidents. The objective of the process is to ensure that normal service operation is restored as quickly as possible and the business impact is minimized.
InsightSCS Incident Management Process PDF
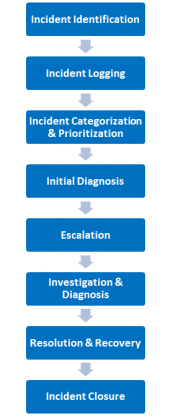
At a very high level, the Incident Management process includes eight process activities:
- Identification – Incidents are detected and reported.
- Logging – All relevant information relating to the nature of the Incident must be documented.
- Categorization & Prioritization – Incidents are categorized and prioritized to facilitate a swift and effective resolution.
- Initial Diagnosis – A diagnosis is carried out to try to discover the full symptoms of the incident.
- Escalation – When the Service Desk cannot resolve the incident, the incident is escalated for further support (functional escalation). If incidents are more serious, the appropriate IT managers must be notified (hierarchic escalation).
- Investigation & Diagnosis – When there is no known solution, the incident is investigated.
- Resolution & Recovery – Once the solution has been found, the issue can be resolved.
- Incident Closure – The Service Desk confirms that the incident is fully resolved and that the user is satisfied and then the incident can be closed.
If the customer can work, the Incident can be resolved. – Anonymous
Problem Management
Overview
Problem Management manages the lifecycle of all Problems. The primary objective of Problem Management are to prevent Incidents from happening, and to minimize the impact of incidents that cannot be prevented. Proactive Problem Management analyzes Incident Records, and uses data/information collected by other IT Service Management processes to identify trends or significant problems. Problem Management includes seven sub-processes:
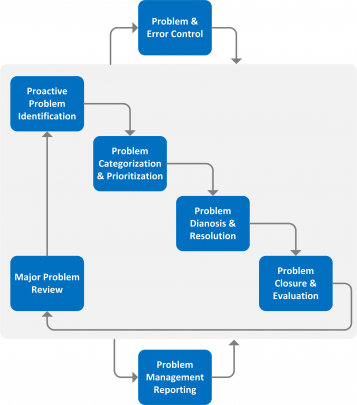
- Proactive Problem Identification – proactively identifying and solving Problems and/or providing suitable workarounds before (further) Incidents recur.
- Problem Categorization & Prioritization – record and prioritize the Problems in order to facilitate a swift and effective resolutions.
- Problem Diagnosis & Resolution – identify the underlying root cause of a Problem and initiate Problem solution. If possible, a temporary Workaround is supplied.
- Problem & Error Control – constantly monitor outstanding Problems so that where necessary corrective measures may be introduced.
- Major Problem Review – review the resolution of a Problem in order to prevent recurrence and learn any lessons for the future.
- Problem Management Reporting – ensure that the other Service Management processes are informed of outstanding Problems, their processing-status and existing Workarounds.
Change Management
Overview
Part of the Service Transition lifecycle, the Change Management process provides a clearly defined procedure to submit, review, approve and schedule requests for IT service changes. The objective of the process is to ensure that changes to the IT environment are carefully considered and reviewed so as to minimize the impact on individuals who use our IT services and to avoid change-related conflicts between our IT services.
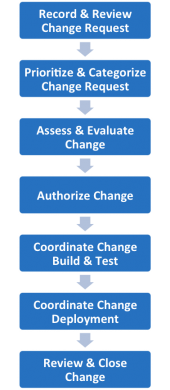
At a very high level, the Change Management Process includes seven sub-process activities:
- Record & Review Change Request – Information from the Request for Change (RFC) is used to create a Change record.
- Prioritize & Categorize Change Request – Changes are categorized according type, size and risk of the change.
- Assess & Evaluate Change – Change Manager will ensure both a technical impact assessment and the risk to the business relative to the change requests are completed by those stakeholders required to assess the Change.
- Authorize Change – Formal authorization is obtained for each Change from a Change authority. The levels of authorization should be judged by the type, size or risk of the Change.
- Coordinate Change Build & Test – Authorized RFCs should be passed to relevant technical groups to build the Changes.
- Coordinate Change Deployment – Authorized RFCs should be passed to the relevant technical groups to deploy the Changes
- Review & Close Change Record – On completion of the Change implementation, the results should be reported for evaluation to the Change Manager. A Change Review (Post Implementation Review) should be carried out to confirm that the Change has met its objectives.
Software Development Lifecycle
A Software Development Lifecycle (SDLC) is essentially a series of steps, or phases that provide a model for the development and lifecycle management of an application or piece of software. The intent of a SDLC process is to help produce a product that is cost-effective, effective, and of high quality.
InsightSCS IT has adopted two different types of SDLC methodologies: waterfall and agile. Although these two methodologies have different ways of organizing the work of software development, with collaboration, planning and process design, we were able to implement a unified solution. Development activities can be tracked and reported on across the enterprise independent of the methodologies used by the development teams.
IT Service Continuity Management
Overview
Part of the Service Design lifecycle, IT Service Continuity Management (ITSCM) manages risks that could seriously impact IT services. ITSCM ensures that the IT service provider can always provide minimum agreed Service Levels, by reducing the risk from disaster events to an acceptable level and planning for recovery of IT services.
InsightSCS Business Continuity Management Policy PDF
At a very high level, the ITSCM includes the following sub process activities:
Initiation – During the initiation stage, policies that specify management intention and objectives should be documented and communicated throughout the organization.
Requirements & Strategies – It is critical to identify and document business requirements for IT Service Continuity in order to ensure that the business can survive a disaster. Business Impact Analysis (BIA) and risk estimate are conducted to develop an IT Service Continuity Strategy.
Implementation – Implementation planning identifies and coordinates the various business and technical plans and deliverables into a cohesive master BCM Plan.
Ongoing Operation – Ongoing operation consists of activities related to maintaining, testing and changing the continuity plans to ensure that they are Fit-for-Purpose over time.
Invocation – Guidance and criteria for making the decision to invoke Business and IT Continuity Plans must be carefully documented in advance.
IT Service Continuity helps us to collaboratively prepare, plan, mitigate and test for the next disaster.
Our Privacy Policy
Overview
Last updated: February 21, 2021 – Download ISCS Privacy Policy v1.1.pdf
This Privacy Policy describes Our policies and procedures on the collection, use and disclosure of Your information when You use the Service and tells You about Your privacy rights and how the law protects You.
We use Your Personal data to provide and improve the Service. By using the Service, You agree to the collection and use of information in accordance with this Privacy Policy.
INTERPRETATION AND DEFINITIONS
Interpretation
The words of which the initial letter is capitalized have meanings defined under the following conditions. The following definitions shall have the same meaning regardless of whether they appear in singular or in plural.
Definitions
For the purposes of this Privacy Policy:
Account means a unique account created for You to access our Service or parts of our Service.
Company (referred to as either “the Company”, “We”, “Us” or “Our” in this
Agreement) refers to InsightSCS Corporation, 3F Aurora Building Alabang-Zapote Road, Cupang, Muntinlupa City, Philippines.
For the purpose of the GDPR, the Company is the Data Controller.
Cookies are small files that are placed on Your computer, mobile device or any
other device by a website, containing the details of Your browsing history on that website among its many uses.
Country refers to: Philippines
Data Controller, for the purposes of the GDPR (General Data Protection
Regulation), refers to the Company as the legal person which alone or jointly with others determines the purposes and means of the processing of Personal Data.
Device means any device that can access the Service such as a computer, a
cellphone or a digital tablet.
Personal Data is any information that relates to an identified or identifiable
individual. For the purposes for GDPR, Personal Data means any information relating to You such as a name, an identification number, location data, online identifier or to one or InsightSCS Page 2 of 9 3F Aurora Building Alabang-Zapote Road, Cupang, Muntinlupa City, Philippines more factors specific to the physical, physiological, genetic, mental, economic, cultural or social identity.
Service refers to the Website.
Service Provider means any natural or legal person who processes the data on behalf of the Company. It refers to third-party companies or individuals employed by the Company to facilitate the Service, to provide the Service on behalf of the Company, to perform services related to the Service or to assist the Company in analyzing how the Service is used. For the purpose of the GDPR, Service Providers are considered Data Processors.
Third-party Social Media Service refers to any website or any social network
website through which a User can log in or create an account to use the Service.
Usage Data refers to data collected automatically, either generated by the use of the Service or from the Service infrastructure itself (for example, the duration of a page visit).
Website refers to Insight Supply Chain Solutions, accessible from https://www.insightscs.com/
You means the individual accessing or using the Service, or the company, or other legal entity on behalf of which such individual is accessing or using the Service, as applicable.
Under GDPR (General Data Protection Regulation), You can be referred to as the Data Subject or as the User as you are the individual using the Service.
COLLECTING AND USING YOUR PERSONAL DATA
Types of Data Collected
Personal Data
While using Our Service, We may ask You to provide Us with certain personally identifiable information that can be used to contact or identify You. Personally identifiable information may include, but is not limited to:
- Email address
- First name and last name
- Phone number
- Address, State, Province, ZIP/Postal code, City
- Bank account information in order to pay for products and/or services within the Service
- Usage Data
When You pay for a product and/or a service via bank transfer, We may ask You to provide information to facilitate this transaction and to verify Your identity. Such information may include, without limitation:
- Date of birth
- Passport or National ID card
- Bank card statement
- Other information linking You to an address
Usage Data
Usage Data is collected automatically when using the Service.
Usage Data may include information such as Your Device’s Internet Protocol address (e.g. IP address), browser type, browser version, the pages of our Service that You visit, the time and date of Your visit, the time spent on those pages, unique device identifiers and other diagnostic data.
When You access the Service by or through a mobile device, We may collect certain information automatically, including, but not limited to, the type of mobile device You use, Your mobile device unique ID, the IP address of Your mobile device, Your mobile operating system, the type of mobile Internet browser You use, unique device identifiers and other diagnostic data.
We may also collect information that Your browser sends whenever You visit our Service or when You access the Service by or through a mobile device.
Tracking Technologies and Cookies
We use Cookies and similar tracking technologies to track the activity on Our Service and store certain information. Tracking technologies used are beacons, tags, and scripts to collect and track information and to improve and analyze Our Service. The technologies We use may include:
- Cookies or Browser Cookies. A cookie is a small file placed on Your Device. You can instruct Your browser to refuse all Cookies or to indicate when a Cookie is being sent. However, if You do not accept Cookies, You may not be able to use some parts of our Service. Unless you have adjusted Your browser setting so that it will refuse Cookies, our Service may use Cookies.
- Flash Cookies. Certain features of our Service may use local stored objects (or Flash Cookies) to collect and store information about Your preferences or Your activity on our Service. Flash Cookies are not managed by the same browser settings as those used for Browser Cookies. For more information on how You can delete Flash Cookies, please read “Where can I change the settings for disabling, or deleting local shared objects?” available at https://helpx.adobe.com/flash-player/kb/disable-local-shared-objectsflash.html#main Where can I change the settings for disabling or deleting local shared objects
- Web Beacons. Certain sections of our Service and our emails may contain small electronic files known as web beacons (also referred to as clear gifs, pixel tags, and single-pixel gifs) that permit the Company, for example, to count users who have visited those pages or opened an email and for other related website statistics (for example, recording the popularity of a certain section and verifying system and server integrity).
Cookies can be “Persistent” or “Session” Cookies. Persistent Cookies remain on Your personal computer or mobile device when You go offline, while Session Cookies are deleted as soon as You close Your web browser. You can learn more about cookies here: “All About Cookies” by Terms Feed.
We use both Session and Persistent Cookies for the purposes set out below:
Necessary / Essential Cookies
Type: Session Cookies
Administered by: Us
Purpose: These Cookies are essential to provide You with services available through the Website and to enable You to use some of its features. They help to authenticate users and prevent fraudulent use of user accounts. Without these Cookies, the services that You have asked for cannot be provided, and We only use these Cookies to provide You with those services.
Cookies Policy / Notice Acceptance Cookies
Type: Persistent Cookies
Administered by: Us
Purpose: These Cookies identify if users have accepted the use of cookies on the Website.
Functionality Cookies
Type: Persistent Cookies
Administered by: Us
Purpose: These Cookies allow us to remember choices You make when You use the Website, such as remembering your login details or language preference. The purpose of these Cookies is to provide You with a more personal experience and to avoid You having to re-enter your preferences every time You use the Website.
Tracking and Performance Cookies
Type: Persistent Cookies
Administered by: Third-Parties
Purpose: These Cookies are used to track information about traffic to the Website and how users use the Website. The information gathered via these Cookies may directly or indirectly identify you as an individual visitor. This is because the information collected is typically linked to a pseudonymous identifier associated with the device you use to access the Website. We may also use these Cookies to test new pages, features or new functionality of the Website to see how our users react to them.
For more information about the cookies we use and your choices regarding cookies, please visit our Cookies Policy or the Cookies section of our Privacy Policy.
Use of Your Personal Data
The Company may use Personal Data for the following purposes:
To provide and maintain our Service, including to monitor the usage of our Service.
To manage Your Account: to manage Your registration as a user of the Service. The Personal Data You provide can give You access to different functionalities of the Service that are available to You as a registered user.
For the performance of a contract: the development, compliance and undertaking of the purchase contract for the products, items or services You have purchased or of any other contract with Us through the Service.
To contact You: To contact You by email, telephone calls, SMS, or other equivalent forms of electronic communication, such as a mobile application’s push notifications regarding updates or informative communications related to the functionalities, products or contracted services, including the security updates, when necessary or reasonable for their implementation.
To provide You with news, special offers and general information about other goods, services and events which we offer that are similar to those that you have already purchased or enquired about unless You have opted not to receive such information.
To manage Your requests: To attend and manage Your requests to Us. For business transfers: We may use Your information to evaluate or conduct a merger, divestiture, restructuring, reorganization, dissolution, or other sale or transfer of some or all of Our assets, whether as a going concern or as part of bankruptcy, liquidation, or similar proceeding, in which Personal Data held by Us about our Service users is among the assets transferred.
For other purposes: We may use Your information for other purposes, such as data analysis, identifying usage trends, determining the effectiveness of our promotional campaigns and to evaluate and improve our Service, products, services, marketing and your experience.
We may share Your personal information in the following situations:
- With Service Providers: We may share Your personal information with Service Providers to monitor and analyze the use of our Service, for payment processing, to contact You.
- For business transfers: We may share or transfer Your personal information in connection with, or during negotiations of, any merger, sale of Company assets, financing, or acquisition of all or a portion of Our business to another company.
- With Affiliates: We may share Your information with Our affiliates, in which case we will require those affiliates to honor this Privacy Policy. Affiliates include Our parent company and any other subsidiaries, joint venture partners or other companies that We control or that are under common control with Us.
- With business partners: We may share Your information with Our business partners to offer You certain products, services or promotions.
- With other users: when You share personal information or otherwise interact in the public areas with other users, such information may be viewed by all users and may be publicly distributed outside. If You interact with other users or register through a Third Party Social Media Service, Your contacts on the Third-Party Social Media Service may see Your name, profile, pictures and description of Your activity. Similarly, other users will be able to view descriptions of Your activity, communicate with You and view Your profile.
- With Your consent: We may disclose Your personal information for any other purpose with Your consent.
Retention Of Your Personal Data
The Company will retain Your Personal Data only for as long as is necessary for the purposes set out in this Privacy Policy. We will retain and use Your Personal Data to the extent necessary to comply with our legal obligations (for example, if we are required to retain your data to comply with applicable laws), resolve disputes, and enforce our legal agreements and policies.
The Company will also retain Usage Data for internal analysis purposes. Usage Data is generally retained for a shorter period of time, except when this data is used to strengthen the security or to improve the functionality of Our Service, or We are legally obligated to retain this data for longer time periods.
Transfer Of Your Personal Data
Your information, including Personal Data, is processed at the Company’s operating offices and in any other places where the parties involved in the processing are located. It means that this information may be transferred to — and maintained on — computers located outside of Your state, province, country or other governmental jurisdiction where the data protection laws may differ than those from Your jurisdiction.
Your consent to this Privacy Policy followed by Your submission of such information represents Your agreement to that transfer.
The Company will take all steps reasonably necessary to ensure that Your data is treated securely and in accordance with this Privacy Policy and no transfer of Your Personal Data will take place to an organization or a country unless there are adequate controls in place including the security of Your data and other personal information.
Disclosure Of Your Personal Data
Business Transactions
If the Company is involved in a merger, acquisition or asset sale, Your Personal Data may be transferred. We will provide notice before Your Personal Data is transferred and becomes subject to a different Privacy Policy.
Law enforcement
Under certain circumstances, the Company may be required to disclose Your Personal Data if required to do so by law or in response to valid requests by public authorities (e.g. a court or a government agency).
Other legal requirements
The Company may disclose Your Personal Data in the good faith belief that such action is necessary to:
- Comply with a legal obligation
- Protect and defend the rights or property of the Company
- Prevent or investigate possible wrongdoing in connection with the Service
- Protect the personal safety of Users of the Service or the public
- Protect against legal liability
Security Of Your Personal Data
The security of Your Personal Data is important to Us, but remember that no method of transmission over the Internet, or method of electronic storage is 100% secure. While We strive to use commercially acceptable means to protect Your Personal Data, We cannot guarantee its absolute security.
Detailed Information On The Processing Of Your Personal Data
The Service Providers We use may have access to Your Personal Data. These third-party vendors collect, store, use, process and transfer information about Your activity on Our Service in accordance with their Privacy Policies.
Analytics
We may use third-party Service providers to monitor and analyze the use of our Service.
Google Analytics
Google Analytics is a web analytics service offered by Google that tracks and reports website traffic. Google uses the data collected to track and monitor the use of our Service. This data is shared with other Google services. Google may use the collected data to contextualize and personalize the ads of its own advertising network. You can opt-out of having made your activity on the Service available to Google Analytics by installing the Google Analytics opt-out browser add-on. The add-on prevents the Google Analytics JavaScript (ga.js, analytics.js and dc.js) from sharing information with Google Analytics about visits activity.
For more information on the privacy practices of Google, please visit the Google
Privacy & Terms web page: https://policies.google.com/privacy
Payments
We may provide paid products and/or services within the Service. In that case, we may use third-party services for payment processing (e.g. payment processors).
We will not store or collect Your payment card details. That information is provided directly to Our third-party payment processors whose use of Your personal information is governed by their Privacy Policy. These payment processors adhere to the standards set by PCI-DSS as managed by the PCI Security Standards Council, which is a joint effort of brands like Visa, Mastercard, American Express and Discover. PCI-DSS requirements help ensure the secure handling of payment information.
PayPal
Their Privacy Policy can be viewed at https://www.paypal.com/webapps/mpp/ua/privacy-full
When You use Our Service to pay a product and/or service via bank transfer, We may ask You to provide information to facilitate this transaction and to verify Your identity.
Children’s Privacy
Our Service does not address anyone under the age of 13. We do not knowingly collect personally identifiable information from anyone under the age of 13. If You are a parent or guardian and You are aware that Your child has provided Us with Personal Data, please contact Us. If We become aware that We have collected Personal Data from anyone under the age of 13 without verification of parental consent, We take steps to remove that information from Our servers.
If We need to rely on consent as a legal basis for processing Your information and Your country requires consent from a parent, We may require Your parent’s consent before We collect and use that information.
Links to Other Websites
Our Service may contain links to other websites that are not operated by Us. If You click on a third party link, You will be directed to that third party’s site. We strongly advise You to review the Privacy Policy of every site You visit.
Changes to this Privacy Policy We have no control over and assume no responsibility for the content, privacy policies or practices of any third party sites or services.
Changes to this Privacy Policy
We may update Our Privacy Policy from time to time. We will notify You of any changes by posting the new Privacy Policy on this page.
We will let You know via email and/or a prominent notice on Our Service, prior to the change becoming effective and update the “Last updated” date at the top of this Privacy Policy.
You are advised to review this Privacy Policy periodically for any changes. Changes to this Privacy Policy are effective when they are posted on this page.
Contact Us
If you have any questions about this Privacy Policy, You can contact us:
- By email: [email protected]
